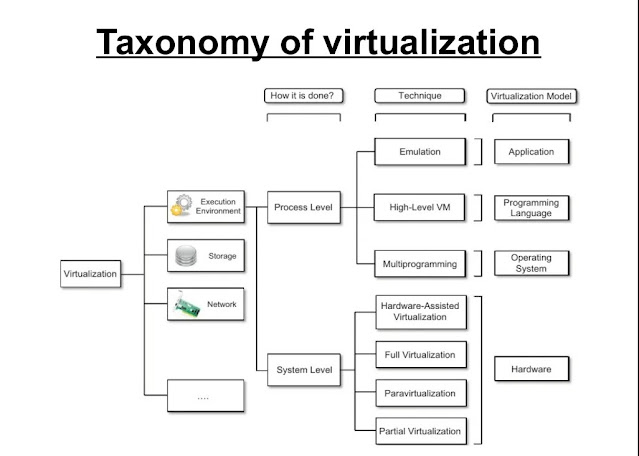
Discuss classification or taxonomy of virtualization at different levels.
Taxonomy of virtualization
- Virtualization is mainly used to emulate the execution environment, storage, and networks. The execution environment is classified into two:
– Process-level – implemented on top of an existing operating system.
– System-level – implemented directly on hardware and does not or minimum requirement of the existing operating system.
OR,
Virtualization covers a wide range of emulation techniques that are applied to different areas of computing. A classification of these techniques helps us better understand their characteristics and use
Virtualization is mainly used to emulate
● Execution Environments: To provide support for the execution of the programs eg. OS, and Application.
○ Process Level: Implemented on top of an existing OS that has full control of the hardware
○ System Level: Implemented directly on Hardware and do not require support from existing OS.
● Storage: Storage virtualization is a system administration practice that allows decoupling the physical organization of the hardware from its logical representation.
● Networks: Network virtualization combines hardware appliances and specific software for the creation and management of a virtual network.
Machine Reference Model
- It defines the interfaces between the levels of abstractions, which hide implementation details. Virtualization techniques actually replace one of the layers and intercept the calls that are directed toward it.
- Hardware is expressed in terms of the Instruction Set Architecture (ISA).
– ISA for the processor, registers, memory, and interrupt management.
- Application Binary Interface (ABI) separates the OS layer from the application and libraries which are managed by the OS.
– System Calls defined
– Allows portabilities of applications and libraries across OS.
API – it interfaces applications to libraries and/or the underlying OS.
- The layered approach simplifies the development and implementation of a computing system.
ISA
ISA has been divided into two security classes:– Privileged Instructions – Nonprivileged Instructions
Nonprivileged instructions
- That can be used without interfering with other tasks because they do not access shared resources. Ex. Arithmetic, floating & fixed point.
Privileged instructions
- They are executed under specific restrictions and are mostly used for sensitive operations, which expose (behavior-sensitive) or modify (control sensitive) the privileged state.
– Behavior-sensitive = operate on the I/O
– Control-sensitive = alter the state of the CPU register.
Privileged Hierarchy:
Security Ring
- Ring-0 is in the most privileged level, used by the kernel.
- Ring-1 & 2 are used by the OS-level services and, R3 in the least privileged level is used by the user. The recent system support two levels:– Ring 0 – supervisor mode – Ring 3 – user mode
OR,
Taxonomy of virtualization
- Virtual machines are broadly classified into two types: System Virtual Machines (also known as Virtual Machines) and Process Virtual Machines (also known as Application Virtual Machines). The classification is based on their usage and degree of similarity to the linked physical machine. The system VM mimics the whole system hardware stack and allows for the execution of the whole operating system Process VM, on the other hand, provides a layer to an operating system that is used to replicate the programming environment for the execution of specific processes.
- A Process Virtual Machine, also known as an application virtual machine, operates as a regular program within a host OS and supports a single process. It is formed when the process begins and deleted when it terminates. Its goal is to create a platform-independent programming environment that abstracts away features of the underlying hardware or operating system, allowing a program to run on any platform. With Linux, for example, Wine software aids in the execution of Windows applications.
- A System Virtual Machine, such as VirtualBox, offers a full system platform that allows the operation of a whole operating system (OS).
- Virtual Machines are used to distribute and designate suitable system resources to software (which might be several operating systems or an application), and the software is restricted to the resources provided by the VM. The actual software layer that allows virtualization is the Virtual Machine Monitor (also known as Hypervisor). Hypervisors are classified into two groups based on their relationship to the underlying hardware. Native VM is a hypervisor that takes direct control of the underlying hardware, whereas hosted VM is a different software layer that runs within the operating system and so has an indirect link with the underlying hardware.
- The system VM abstracts the Instruction Set Architecture, which differs slightly from that of the actual hardware platform. The primary benefits of system VM include consolidation (it allows multiple operating systems to coexist on a single computer system with strong isolation from each other), application provisioning, maintenance, high availability, and disaster recovery, as well as sandboxing, faster reboot, and improved debugging access.
- The process VM enables conventional application execution inside the underlying operating system to support a single process. To support the execution of numerous applications associated with numerous processes, we can construct numerous instances of process VM. The process VM is formed when the process starts and terminates when the process is terminated. The primary goal of process VM is to provide platform independence (in terms of development environment), which implies that applications may be executed in the same way on any of the underlying hardware and software platforms. Process VM as opposed to system VM, abstracts high-level programming languages. Although Process VM is built using an interpreter, it achieves comparable speed to compiler-based programming languages using a just-in-time compilation mechanism.
- Java Virtual Machine (JVM) and Common Language Runtime are two popular examples of Process VMs that are used to virtualize the Java programming language and the.NET Framework programming environment, respectively.

Comments
Post a Comment